Machine learning is declining the risks of phishing attacks, but the number of such attacks are still on the rise, finds the 24th edition of the Microsoft Security Intelligence Report (SIR).
Microsoft analyzes over 6.5 trillion security signals every day to get a wide and unique perspective into latest trends in the cybersecurity arena. The company has been releasing the security intelligence report for more than a decade now to share its expert insights with the enterprises.
The SIR this year is reflected on security events in 2018, including overview of security landscape, lessons learnt from it, and best practices that need to be followed. Some of the cybersecurity trends in 2018 included rise in cryptocurrency mining and supply chain compromises, decline in ransomware, and more.
Attackers are increasingly mining cryptocurrency in the background of user systems, without their permission and awareness. This activity significantly consumes bandwidth and causes security risks to users.
Having said that, let’s have a deep dive into the key findings of the Microsoft’s latest security report.
Key takeaways from Microsoft Security Intelligence Report:
1. Ransomware encounters declined significantly in 2018
Ransomware attacks like WannaCrypt and Petya were the biggest security events in 2017. Such attacks locks or encrypt computers and then demands money from users to restore access. It was anticipated that these ransomware attacks will increase in future.
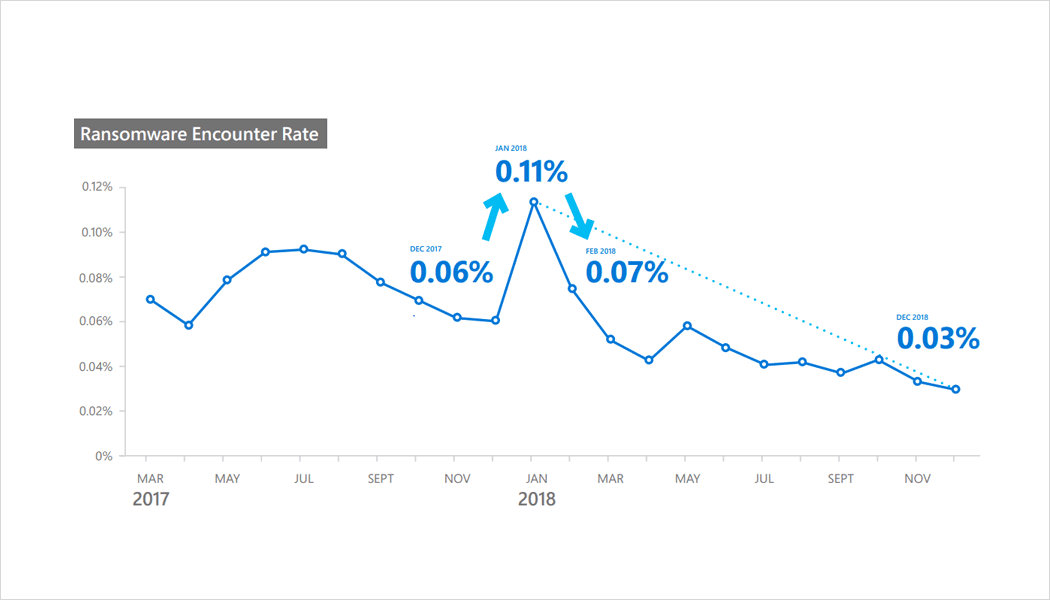
However, the latest report says that ransomware encounter rates have declined by around 60% between March 2017 and December 2018.
The main reason behind this decline is improved detection and education among enterprises. This made it tough for cybercriminals to get what they were intending.
Highest ransomware encounter rate:
The highest average ransomware encounter rate per month were found in Ethiopia (0.77%), followed by Mongolia (0.46%), Cameroon (0.41%), Myanmar (0.33%), and Venezuela (0.31%).
Lowest ransomware encounter rate:
On the other hand, the lowest ransomware encounter rates per month were found in Ireland (0.01%), Japan (0.01%), the United States (0.02%), United Kingdom (0.02%), and Sweden (0.02%).
2. Cryptocurrency mining is becoming prevalent
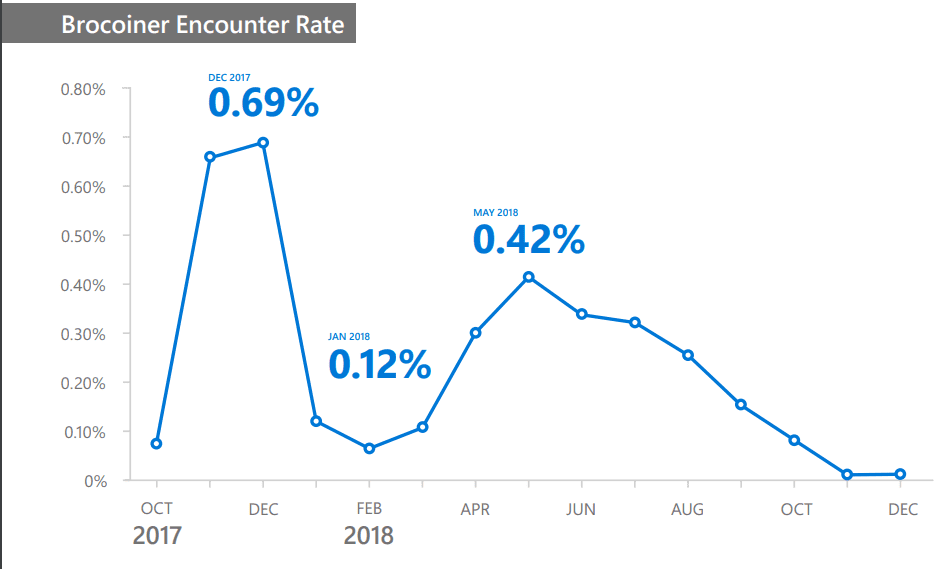
Since the cybercriminals found it difficult to conduct ransomware attacks, they shifted their efforts to cryptocurrency mining. As a result, the cryptocurrency mining is increasing.
While the average ransomware encounter rate in 2018 was just 0.05%, the same for cryptocurrency coin mining encounter was 0.12%.
Cryptocurrencies like Bitcoin and Ethereum work as digital money and can be used anonymously. However, the cryptocurrencies require users to perform some calculations that are resource intensive. While new cryptocurrency coins are released very frequently these days, the calculations are becoming more difficult.
Mining of top cryptocurrencies like Bitcoin is almost impossible, if the immense computing resources are not accessible. As a result, the cybercriminals have turned to a malware that helps them gain access to the computers of victims and then mine cryptocurrency coins. By this way, they can leverage the processing power of hundreds of thousands of computers, rather than one or two.
Highest cryptocurrency mining encounter rate:
Ethiopia (5.58%), Tanzania (1.83%), Pakistan (1.47%), Kazakhstan (1.24%), and Zambia (1.13%) are the five locations with the highest cryptocurrency coin mining encounter rates in 2018.
Lowest cryptocurrency mining encounter rate:
The lowest average monthly coin mining encounter rate was approx. 0.02% in 2018. Ireland, Japan, the US, and China were the locations with lowest rate during the period.
3. Browser-based cryptocurrency mining comes to the scene
Typically, the cryptocurrency miners are installed on the computers of victims in the form of malware. But a new kind of threat has come to scene, where the malware is based entirely within web browsers, which doesn’t need to be installed on the computers.
What cybercriminals are doing is offering a number of services that promise website owner to monetize traffic to their websites without need of advertising. The site owners are asked to add JavaScript code to their webpages. This code starts mining cryptocurrency in the background. When a website is compromised, the attackers can take advantage of the users who visit that website.
These are browser-based cryptocurrency miners that don’t need to compromise the computers. Such miners can impact the computer performance and waste electricity while the users browse the compromised websites.
According to the report, Brocoiner was the most prevalent browser-based cryptocurrency in 2018.
4. Software supply chains are at risk
Attackers try to compromise the development or update process of a legitimate software to gain access to the software and systems of people who use the compromised software.
By injecting the malicious code into the software, attackers can easily gain the same trust and permissions as the software. This has become a primary concern for IT leaders as these attacks are increasing and can make the enterprise IT departments vulnerable.

For example, the first major software supply chain in 2018 was found in March. Microsoft’s Windows Defender ATP blocked a massive campaign that was delivering Dofoil trojan, also called Smoke Loader.
The attackers had replaced the update package of an application with malicious code. This trojan had carried a coin mining payload and exhibited advanced cross-process injection techniques, persistence mechanisms, and evasion methods.
Windows Defender Antivirus had blocked over 400k infection attempts, in the first 12 hours of the campaign.
Suggested reading: Carelessness of employees leading to enterprise security concerns: Microsoft report
5. Email phishing is still a preferred attack method
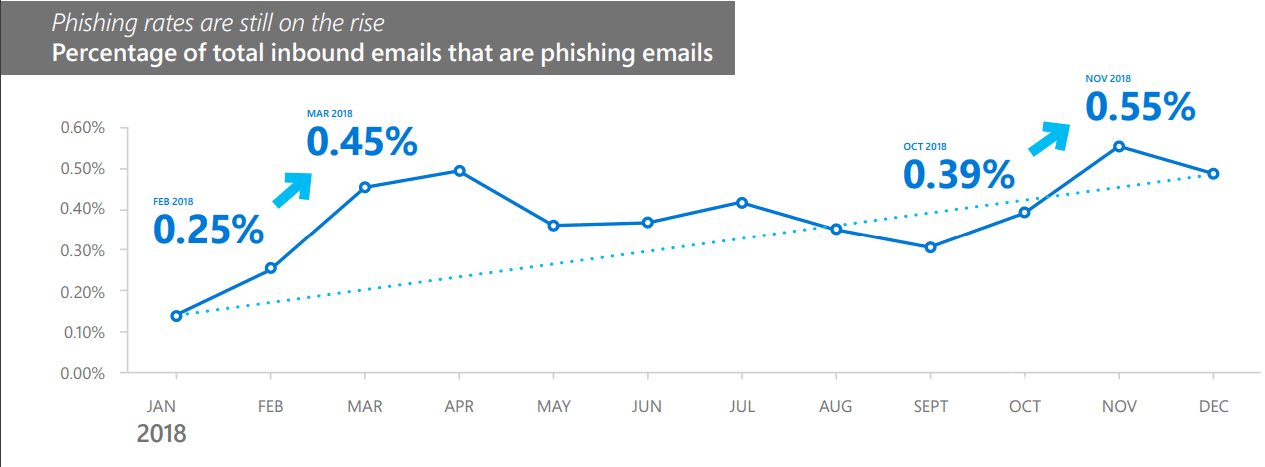
Office 365 is the most popular enterprise productivity available out there. Microsoft said that it analyzes over 470 billion email messages per month to scan phishing and malware. In 2018, the phishing messages in inbound emails increased by 250%.
It shows that email phishing is still one of the most preferred attack methods for cybercriminals. Microsoft is rapidly strengthening the email security with anti-phishing protection, detection, and investigation. But, since the emails involve human decisions and judgement, it is a problem to completely get rid of the phishing.
Suggested reading: Office 365 is now the most effective solution at mitigating phish emails
Email phishing lures can come in these forms:
- Domain spoofing— the email message domain is an exact match with the original domain name.
- Domain impersonation— the email message domain is a look alike of the original domain name.
- User impersonation— the email message appears to come from someone you trust.
- Credential phishing links—the email message contains a link to a page that resembles a login page for a legitimate site, so users will enter their login credentials.
- Phishing attachments—the email message contains a malicious file attachment that the sender entices the victim to open.
- Links to fake cloud storage locations— the email message appears to come from a legitimate source and entices the user to give permission and/or enter personal information such as credentials in exchange for accessing a fake cloud storage location.
For full Microsoft Security Intelligence Report (SIR), click here. Microsoft has also created an interactive website to allow users dig into the data specific to the regions.